Technology has become a fundamental part of our daily life. Nowadays, every modern process uses computers to perform their actions. Until the late 1980s, all college assignments were done either by hand, or by typewriter. Today, in the twenty-first century, everything is done on computers. In the last century, letters and telegrams were used to communicate written material over long distances. However, today just one click is enough to send a message to the other side of the world. Technology is ubiquitous; now all banks and online stores place absolute trust in the internet to make bank transfers of often astonishingly large monetary sums. However, it is not all a bed of roses for the internet. Just as every thesis has its antithesis, the internet world found its executioner in computer viruses. There are many unfortunate people who, because of computer viruses, end up losing everything, from their images and music, to valuable works, and even thesis projects. We all know about the existence of viruses, but very few of us really understand how they work, how they propagate through the web, and the magnitude of the effects of viruses on our devices and our lives.

Hated by all, the computer virus is the number one enemy of all who own a laptop, a computer, tablet, and even a smartphone. Its construction is simple but can be devastating. The virus is a piece of software based on various characteristics and with innumerable “themes.” In the same way as a biological virus, it attacks the host (in this case, the computer) and begins to infect many others to increase its reach. Basically, the virus is hidden in a program or document and is released when these files are executed. This plague of the electronic age emerged in the 1970s, initially only for programmers to demonstrate their skills. However, it ended up becoming a very lucrative criminal activity. Today, there are malware (malicious software) being spread by email or infected sites, and even by artificial intelligence, which simulates real conversations in chats to convince the victim to click on a contaminated link.1
The malicious software can be of various types, of which two are the most common in the world of computer science. Perhaps the best known type of malware is the Trojan Horse, which is as treacherous as its namesake in Greek mythology. A Trojan typically disguises itself as a normal and benevolent application during its installation. The users who receive the Trojans are convinced to install them and execute them because they have received them from a trusted source. Once executed, a Trojan can cause severe damage, such as capture of bank passwords, credit card data, social network passwords, etc. Another common group of malware are worms, a particularly harmful subclass of viruses that are distinguished by their ability to spread without human action, using all communication capabilities available in a device to self-distribute.2 Worms replicate themselves inside an infected device, creating thousands of copies of itself, in order to spread more quickly and prevent an antivirus from removing them before causing damage and contaminating other devices. Worms are also used to open ports on the infected user’s device, allowing a hacker total remote control of all available resources on the infected device.3
A colossal number of viruses churn through the internet, but among all the stories that can be told about viruses, there is one that stands out among all the others: the virus “I Love You,” the one that took advantage of the innocence of a secret message of love that destroyed 45 million computers! The story behind the catastrophic message created by Onel de Guzman, will surprise many people, including you. Without further ado, the story of one of the most lethal thesis projects in history: I Love You.4

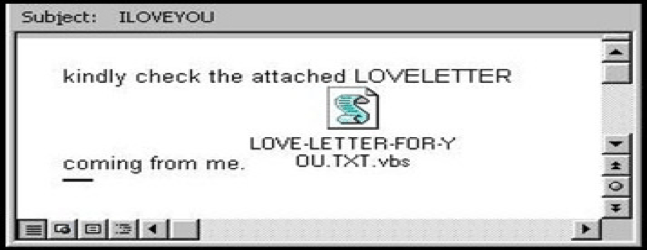
On May 4, 2000 computer networks around the world were invaded by the virus that has until today earned the title of fastest propagation invader. In a matter of hours, the “Love Bug,” as the virus became known, infected more than three million machines. It came with a message in which both the subject “I Love You” and the attachment “Love-Letter-For-You” appealed to the curiosity of the recipient. To further disarm the victim’s defenses, the e-mail came almost always in the name of a friend or acquaintance.6 Although it had no destructive load, the love letter caused deep havoc by producing an unprecedented e-mail branch that congested servers around the world, causing billions of dollars of losses for companies around the world. According to the consulting company Computer Economics, the losses were around twelve million dollars.7 Not even the “Code Red” and “Sircam” viruses, which in 2001 caused an injury of 3 million and 1.5 million dollars, respectively, overcame this virus that certainly entered into history as the most devastating of the global network of computers.8
“The teachers did not like my work, they rejected my thesis. They said it was against the policy of the faculty and everything just because I used the word steal instead of access. It was a simple matter of vocabulary,” recalls the “Clyde Barrow” of computer hacking and author of one of the greatest computer disasters in history.9

The truth is that his idea was brilliant, as well as perverse. If the virus “I love you” spread so quickly, it was because everyone liked the idea of receiving an anonymous love letter. The famous love letter was the product of the disgust of a disgruntled student with his faculty, the revenge of Onel, because they rejected his thesis. Clerks, stockbrokers, politicians, firemen, or journalists, people here and there, opened the message of the supposed admirer or secret lover who began his letter proclaiming his love. Just by clicking it, the program created by Onel de Guzman began to work, that is, to eliminate. First, the virus infected the computer itself and destroyed the information on the hard disk. Then the virus forwarded the electronic message to all the addresses that the receiver had stored, in an unstoppable chain. Within twenty-four hours three million computers had been infected and within a week there were already more than 45 million computers unusable.10 Probably the final number of victims of what some experts still qualify as the most virulent, devastating, and costly virus in history, will never be known. The teachers of the AMA School of Computer Science could not believe it when, three months after receiving the thesis of their model student, they realized that the virus that was going around the world worked exactly as Onel had explained in his dissertation. His thesis, which he called “The Trojan Horse,” still circulates on the Internet today and is the bible for many computer hackers, teachers, students, and curious people.11
What happened to the author of one of the most serious cyber catastrophes in history? Absolutely nothing. The Government of the Philippines had with Onel case its first cybercrime in its history. The Philippine authorities found a total absence of cybercrime legislation with which to prosecute the alleged perpetrator. After the appearance of the virus “I love you,” the government of the Philippines created a law on computer crimes, but it could not be applied retroactively and therefore did not affect the author of the love letter.[12: Robert Frank, “Lacking Laws, The Philippines Throws Out ‘Love Bug’ Case,” Wall Street Journal – Eastern Edition, (August 22, 2000): 20.]

Onel de Guzman just needed one computer and an internet connection to be able to invade more than 45 million computers in just one week.12 De Guzman’ virus was so powerful that it was even able to penetrate one of the most powerful cybernetic systems in the world, the Pentagon of the United States of America. Yes, it is no joke, a college student was able to infect four classified military systems of one of the safest and most sheltered facilities on the planet.13 If the Philippine was able to crash one of the most powerful systems in the world, monitor financial accounts, steal personal information and messages, we must be ever vigilant before we casually click on any email attachment.14 A computer virus, like a biological one, does not distinguish social condition, economic power, political position, or any other difference. They are there, waiting for a click, which will allow them to do what they do best: destroy everything in their way. Let’s be always alert.
- Funk & Wagnalls New World Encyclopedia, August 2016, s.v. “Computer Virus.” ↵
- Roberta D. Anderson, “Viruses, Trojans, and Spyware, Oh My; The Yellow Brick Road to Coverage in the Land of Internet Oz ,” Tort Trial & Insurance Practice Law Journal no. 2 (June 2013): 529. ↵
- Salem Press Encyclopedia Of Science, January 2017, s.v.”Computer viruses and worms,” by Linda Volonino. ↵
- “I Love You’ virus,” Journal of Property Management 70, no. 2 (March 2005): 9. ↵
- Adam Cohen, “School for Hackers,” Time Magazine 155, no. 21 (May 2000): 59. ↵
- Mark Ward, “A decade on from the I Love You bug,” BBC News (May 2010), 5. ↵
- Bob Edwards, “Analysis: Projected cost of damages caused by the ‘Love Bug’ computer virus,” Morning Edition (May 2000): 23-24. ↵
- Keith A. Rhodes, Information Security: Code Red, Code Red II, and SirCam Attacks Highlight Need for Proactive Measures (Washington D.C.: U.S. General Accounting Office, 2001), 23-24. ↵
- Rajiv Chandrasekaran, “Student Proposed Virus in Thesis; ‘Love Bug’ Probe Focuses on Filipino College Senior,” The Washington Post, (May 2000): 7-8. ↵
- Frank Prince, “Love Bug’ Redux: Keeping Alert to Danger,” Community Banker Journal, (June 2000): 45. ↵
- Rajiv Chandrasekaran, “Student Proposed Virus in Thesis; ‘Love Bug’ Probe Focuses on Filipino College Senior,” The Washington Post, (May 2000): 7-8. ↵
- Bob Edwards, “Analysis: Projected cost of damages caused by the ‘Love Bug’ computer virus,” Morning Edition (May 2000): 23-24. ↵
- Mark Lander, “A Filipino Linked to ‘Love Bug’ Talks About His License to Hack,” The New York Times, (October 21, 2000): 1. ↵
- Karen D. Loch,”Threats to Information Systems: Today’s Reality, Yesterday’s Understanding,” MIS Quarterly 16, no. 2 (June 1992): 177. ↵


80 comments
Kenneth Gilley
Wow! It is amazing that a Filipino college student was able to wreak so much havoc. To think that just clicking on a file in an email could destroy a computer’s hard drive and send the virus to all of the other computers that the infected computer had in its address book. It is a shame that they were unable to punish Onel de Guzman for his treachery.
Emmanuel Diaz
I’m actually quite fascinated at how a simple message, from someone anonymous, tricked many into being curious rather than being cautious and opening up the message and allowing for the virus to get into their computer and revealing their personal information. Though, Onel did this out of anger, you have to say that it was a bit much at what he did just because his thesis was denied but i feel without him there would have been a setback to such an early yet destructive flaw of the internet without him and his “I love you” encryption to the world. We love you too, Onel!
Great article!
Kathryn Martinez
We live in a time period where the majority of us have our lives connected to the internet. Some even have their careers attached to working with the internet and the simple fact that one person could ruin that with a simple mistake is insane. Without the development of the internet, our lives wouldn’t be as advanced as they are today. We wouldn’t even be reading this article without the internet, so the fact that Onel Guzman allowed for a virus to spread is insane.
Elisa Nieves
Quite frankly, I’m stunned. I can’t believe that a simple little configuration was able to destroy the hard drives of so many peoples’ computers and spread so fast. I think Onel de Guzman is incredibly immature for letting loose such a virus. I’ll admit it’s really cool that he was able to put it together, but I believe it is wise to keep some things from being put in use. This, for example, is definitely one of them. I also think, however, that Onel de Guzman’s teacher should have been more cautious with the things his student was doing by watching him closely and taking away his availability to let loose his virus once it was formed.
Briana Montes
Its crazy how technology has helped us and hurt us at the same time. Computer viruses are annoying and scary because they can take over your information and use it. This article was mind opening because it can happen to anyone now a days. How all our personal information can be put in the wrong hands. Great article to read!
Sabrina Doyon
Honestly, I don’t blame the guy. He worked really hard writing his thesis, turned it in proudly, and got rejected. His revenge, however, was a bit detrimental. He caused many companies to lose money and servers to be clogged. All because he was rejected by his professors. In the quote, you can almost taste the petty. He is very clever, using emotion and affection to fool thousands of people into contracting his virus.
Andrew Gonzales
Its amazing to think that out of all the advances of technology it can all be brought down by a “virus”. Its crazy that they are still an issue and that a kid brought down over 44 million computers with just one “love note”. A great told story one that I’ll never forget.
Sharriah Martinez
the internet is a scary place. It is crazy by just a touch of a button your identity can be gone all of your personal information can go to someone else. The numbers are just outrageous.. twelve million dollars, forty five million computers unstable in a weeks time . Onel Guzman was a name i never knew but will never forget. It is crazy that it ended up being a accident because he was just trying to profess his love to someone. crazy. my mind is boggled.
Octaviano Huron
It is very scary to know that one click of a mouse or push of a button can wipe out everything about a person’s identity. Computer viruses are not only annoying; they can infiltrate a person’s life and can cause massive devastation. When applying for scholarships in high school, I had learned about scams and fake websites that asked for money in order to be considered for some sort of “prize” that would supposedly pay for tuition. Overall, this was a very well-written article, and I hope this article teaches people to be safe online.
Maya Mani
Technology is both a blessing and a curse. While it has offered numerous advantages to our society, it also has introduced new threats. So much was happening in this story and it just became scarier and scarier. Something has seemingly harmless as opening a letter, ended up being one of the worst decisions to make. Virus’s seem to be everywhere these days. This article is frightening to read because realistically, it could happen to anyone.